Armitage Package Description
Armitage is a scriptable red team collaboration tool for Metasploit that visualizes targets, recommends exploits, and exposes the advanced post-exploitation features in the framework.
Through one Metasploit instance, your team will:
- Use the same sessions
- Share hosts, captured data, and downloaded files
- Communicate through a shared event log.
- Run bots to automate red team tasks.
Armitage is a force multiplier for red team operations.
Source: http://www.fastandeasyhacking.com/manual#0
Armitage Homepage | Kali Armitage Repo
- Author: Strategic Cyber LLC
- License: BSD
Tools included in the armitage package
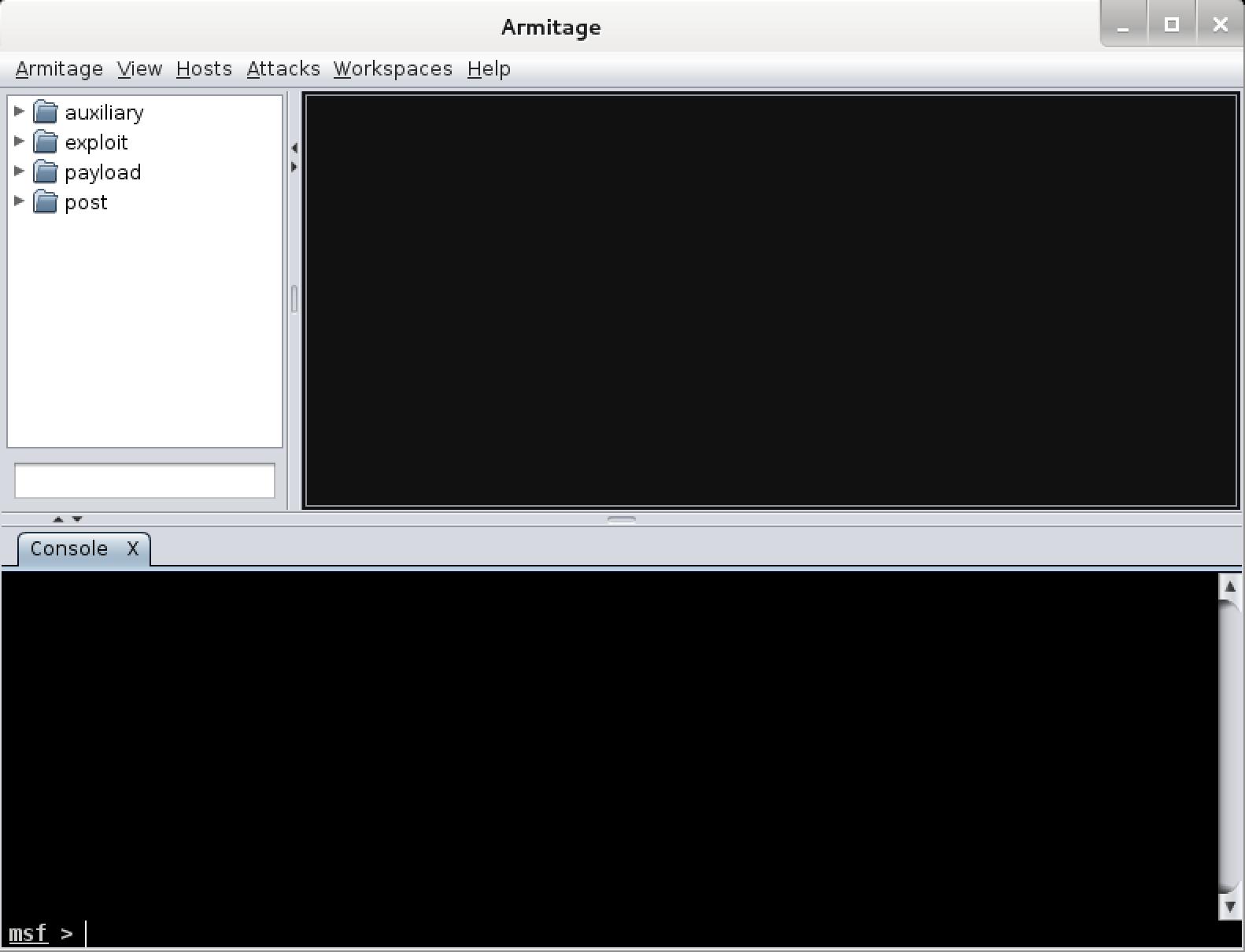
armitage – Red team collaboration tool
Armitage is a scriptable red team collaboration tool for Metasploit that visualizes targets, recommends exploits, and exposes the advanced post-exploitation features in the framework.
teamserver – Armitage Teamserver component
[email protected]:~# teamserver
[*] You must provide: <external IP address> <team password>
<external IP address> must be reachable by Armitage
clients on port 55553
<team password> is a shared password your team uses to
authenticate to the Armitage team server
armitage Usage Example
[email protected]:~# armitage
[*] Starting msfrpcd for you.
teamserver Usage Example
Start teamserver on the external IP (192.168.1.202) and set the server password (s3cr3t):
[email protected]:~# teamserver 192.168.1.202 s3cr3t
[*] Generating X509 certificate and keystore (for SSL)
[*] Starting RPC daemon
[*] MSGRPC starting on 127.0.0.1:55554 (NO SSL):Msg...
[*] MSGRPC backgrounding at 2014-05-14 15:05:46 -0400...
[*] sleeping for 20s (to let msfrpcd initialize)
[*] Starting Armitage team server
[-] Java 1.6 is not supported with this tool. Please upgrade to Java 1.7
[*] Use the following connection details to connect your clients:
Host: 192.168.1.202
Port: 55553
User: msf
Pass: s3cr3t
[*] Fingerprint (check for this string when you connect):
a3b60bef430037a6b628d9011924341b8c09081
[+] multi-player metasploit... ready to go